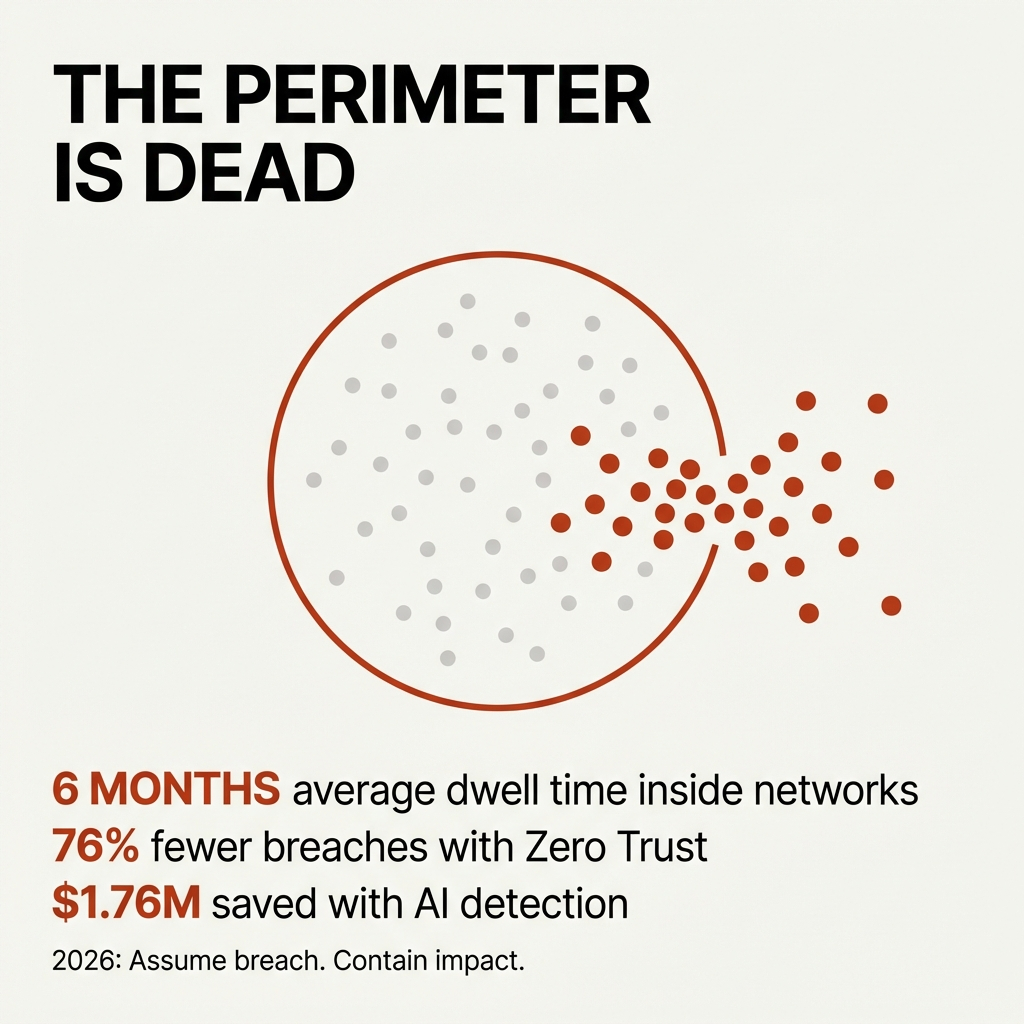
The perimeter is dead.
I don’t mean that as a dramatic opening. I mean it as an operational reality that most organizations still haven’t internalized.
By 2026, Zero Trust Architecture isn’t aspirational. It’s the baseline expectation for organizations operating in hybrid and cloud environments. The shift isn’t happening because of compliance mandates or vendor marketing. It’s happening because static perimeters have failed to keep pace with how threats actually move.
The average dwell time for an intruder inside a network is over six months. That means attackers are already inside, moving laterally, escalating privileges, and exfiltrating data while your perimeter defenses report green.
The question isn’t if your organization will be breached. It’s what happens when it is.
The Shift From Prevention to Containment
Organizations implementing Zero Trust AI Security reported 76% fewer successful breaches and reduced incident response times from days to minutes. That’s not because they prevented every attack. It’s because they designed systems that limit blast radius when attacks succeed.
Here’s what changed in their approach:
They stopped trusting credentials alone.
In 2026, identity is the most targeted attack vector. 84% of organizations experienced identity-related breaches in 2025. Stolen credentials are no longer edge cases. They’re the primary entry point.
Zero Trust assumes credentials will be compromised. So it adds layers: device health checks, location analysis, continuous risk scoring, and conditional access policies. If an attacker gets a username and password, they still can’t move.
I’ve seen environments where stolen credentials were actively being tested by attackers, and nothing happened. The system simply didn’t allow unsafe access paths.
They segmented access by default.
In perimeter-based models, once you’re inside, you’re trusted. One compromised account often becomes a bridge into email, file shares, admin portals, and SaaS applications.
In Zero Trust environments, every application has defined owners, scoped roles, and enforced boundaries. If one system is breached, it doesn’t automatically grant access to everything else.
This isn’t theoretical. Breaches spanning multiple environments cost an average of $5.05 million compared to $4.01 million for on-premises incidents. They also last longer—276 days versus 217 days.
Containment design reduces both cost and duration.
They made detection as critical as prevention.
Organizations using AI-powered security systems in 2024 detected and contained breaches 108 days faster than others, saving an average of $1.76 million per breach.
The difference wasn’t better firewalls. It was better visibility.
When you assume breach, detection becomes a primary control. You’re not asking “did they get in?” You’re asking “where are they now, and how do we stop them from moving further?”
That requires continuous monitoring, behavior analytics, and automated response workflows that don’t wait for human approval.
What Proactive Resilience Actually Looks Like
Resilience isn’t about recovering from incidents. It’s about designing systems that degrade gracefully when something fails.
Here’s what that looks like in practice for a mid-sized organization:
Access is evaluated continuously, not once at login.
Traditional authentication happens at the front door. You enter credentials, pass MFA, and you’re in for the session.
Zero Trust evaluates access throughout the session. If device posture changes, if location shifts, if behavior deviates from baseline patterns, access is re-evaluated in real time.
This means compromised sessions get cut off before damage occurs.
Admin privileges are time-bound and scoped.
Permanent admin access is one of the highest-risk patterns in IT. 72% of breaches involve the exploitation of privileged credentials.
In resilient environments, admin rights are granted just-in-time for specific tasks and automatically revoked when the task is complete. No one holds standing privileges that can be stolen and abused indefinitely.
Devices are treated as part of the identity layer.
Credentials can be phished. Devices are harder to fake.
Zero Trust architectures require managed, compliant devices for access to sensitive systems. If an attacker steals credentials but doesn’t control a trusted device, they can’t authenticate.
This single control blocks the majority of credential-based attacks.
Third-party access is isolated and monitored.
30% of breaches in 2025 involved third-party vendors—double the rate from the previous year. Most of those breaches happened because vendors had broad, persistent access to internal systems.
Resilient organizations extend Zero Trust principles to partner ecosystems. Vendors get scoped access, time-limited sessions, and monitored activity. When the engagement ends, access ends automatically.
Why Most Organizations Still Operate Reactively
The shift to assume-breach architecture isn’t technical. It’s conceptual.
Most organizations still operate under the assumption that breaches are preventable events. They invest in perimeter defenses, run annual security awareness training, and treat incidents as failures rather than inevitabilities.
Here’s what that looks like on the ground:
Recurring known problems.
If the same security gaps keep appearing—weak passwords, unpatched systems, excessive permissions—that’s not bad luck. That’s unresolved design debt.
Reactive organizations close tickets. Proactive organizations eliminate root causes.
Hero-driven stability.
If your security posture depends on one person remembering to check logs, review access, or catch anomalies, you’re operating reactively.
When that person is out, the gaps appear immediately.
Proactive environments automate visibility and response. Stability doesn’t live in someone’s head. It’s built into the system.
Manual governance.
If leadership relies on spreadsheets and email chains to understand who has access to what, you’re discovering risk late.
In assume-breach environments, governance is embedded. Dashboards, alerts, and automated reports exist by default. Evidence is generated as a byproduct of normal operations, not assembled during audits.
The Real Cost of Delayed Adoption
Breach costs are 38% higher for organizations without Zero Trust implementation. The average breach costs $5.2 million globally in 2026. Organizations without AI or automation paid $5.52 million on average, while those using them extensively reduced costs to $3.62 million.
But the financial impact is only part of the equation.
The real cost shows up in:
**Delayed projects.** When security incidents consume engineering time, product roadmaps slip. Strategic initiatives get deprioritized. Growth slows.
**Leadership blind spots.** When visibility requires manual assembly, executives make decisions based on incomplete or outdated data. Risk becomes invisible until it’s catastrophic.
**Talent burnout.** When stability depends on heroics, your best people absorb the system’s design flaws with their time and energy. Eventually, they leave.
**Regulatory exposure.** Breaches that could have been contained become reportable incidents. Fines, audits, and reputational damage follow.
The organizations that adopt assume-breach architecture early don’t just reduce incident frequency. They reclaim capacity, improve decision quality, and build environments where security becomes routine instead of reactive.
What Leadership Needs to Understand
Zero Trust isn’t a product you buy. It’s a design philosophy you implement across identity, access, devices, applications, and data.
65% of organizations plan to replace VPN services within the year—a 23% jump from last year. 81% are actively implementing Zero Trust frameworks. The shift is already happening.
But adoption without understanding creates new problems. Organizations that bolt Zero Trust onto reactive processes end up with more complexity and the same vulnerabilities.
Here’s what actually needs to change:
Accountability precedes technology.
Before implementing new security controls, assign ownership. Who is responsible for this system six months from now when something breaks? If no one can answer that clearly, the technology won’t solve anything.
Standardization enables resilience.
Zero Trust requires consistent identity, device management, and access policies. You can’t enforce least-privilege access if every application has different authentication methods and every user has custom permissions.
Standardizing the foundation creates the capacity to handle exceptions safely.
Visibility must be automatic.
If security posture requires manual reporting, you’re always operating on stale data. Real-time dashboards, automated alerts, and continuous monitoring aren’t nice-to-haves. They’re prerequisites for assume-breach architecture.
Governance produces evidence naturally.
If compliance requires people to remember to document, it’s fragile. If compliance is embedded in workflows, evidence is unavoidable.
Access reviews, device compliance reports, and audit trails should be system-generated byproducts, not scrambled together during audits.
The Path Forward
The 2026 cybersecurity landscape doesn’t reward organizations that build higher walls. It rewards organizations that assume the walls will fail and design accordingly.
That means:
**Treating identity as infrastructure.** Not just usernames and passwords, but device health, location context, and continuous risk evaluation.
**Segmenting access by default.** Every application, every data store, every administrative function gets scoped permissions and monitored activity.
**Automating detection and response.** Humans can’t keep pace with modern threats. Systems need to identify anomalies and contain them without waiting for approval.
**Extending Zero Trust to partners.** Third-party risk is doubling year over year. Vendor access needs the same rigor as employee access.
**Embedding governance into operations.** Compliance shouldn’t be a separate effort. It should be a natural output of well-designed systems.
This isn’t about perfection. It’s about containment.
Breaches will happen. Credentials will be stolen. Devices will be compromised. The question is whether your environment limits the damage or amplifies it.
Organizations that answer that question correctly don’t just survive incidents. They operate with confidence, knowing their systems are designed to degrade gracefully under pressure.
That’s what proactive resilience looks like in 2026.